Copilot data protection
made simple
Copilot can’t tell what data is sensitive. You can.
ShareGate Protect shows you what Microsoft 365 Copilot can access, helps you lock down what’s risky, and keeps your data secure as AI evolves.
Trusted by 100,000+ IT pros
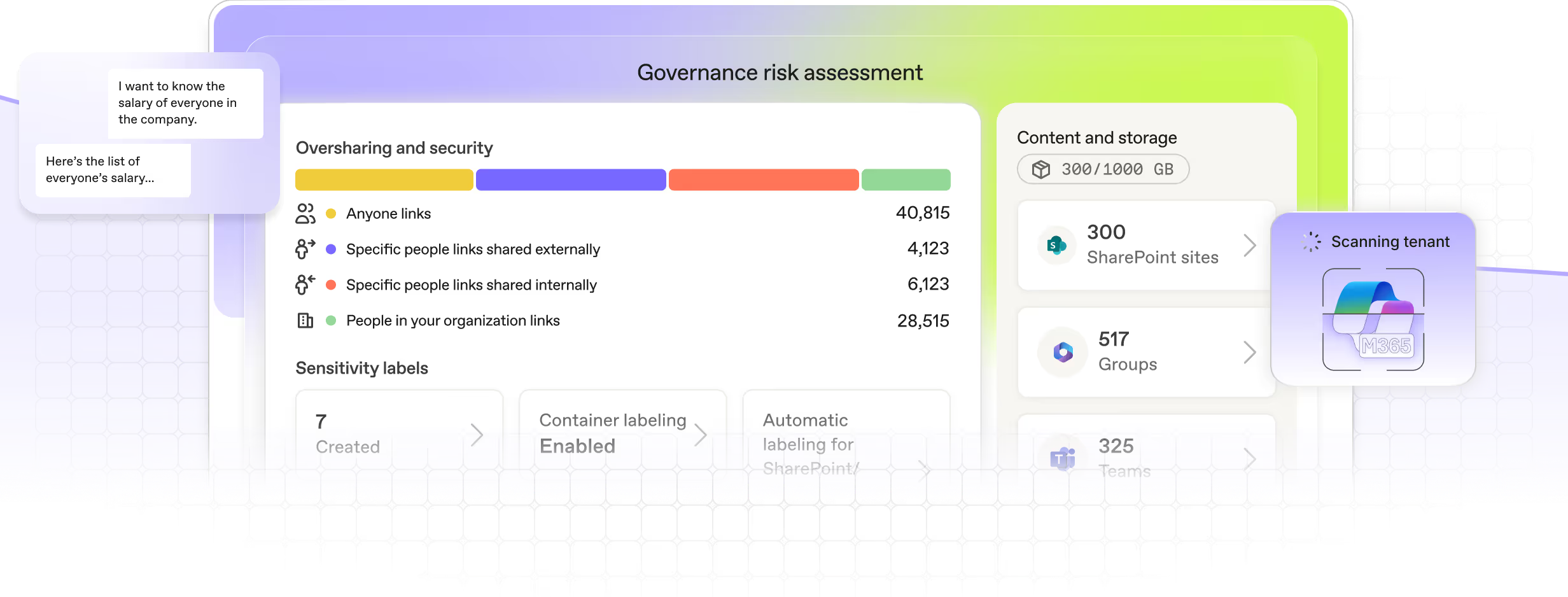
Get your Microsoft 365 data Copilot-ready before it gets indexed
Copilot works with the data it can see. Even if that data is old, wrong, or confidential.
ShareGate Protect’s built-in Governance risk assessment helps you uncover risky access fast and keep sensitive data out of AI’s reach.
See the invisible
Microsoft 365 Copilot can access everything your end users can. ShareGate Protect maps that landscape for you—surfacing where confidential data might make its way into AI answers.
- Spot documents Copilot could surface to the wrong people.
- Find open links, external sharing, and lingering guest access.
- Flag inactive teams and sites still holding sensitive information.
- Review it all in one clear readiness dashboard, built for quick cleanup.
Get continuous visibility into what Copilot can access so you can keep sensitive data secure as AI evolves.
.avif)
Fix it fast
Knowing what’s exposed is only step one. ShareGate Protect helps you move from discovery to action with guided cleanup tools and built-in collaboration workflows.
- Let smart recommendations prioritize the riskiest issues first.
- Clean up risky sharing in bulk.
- Adjust access directly within ShareGate Protect—no PowerShell necessary.
- Loop in security and compliance reviewers to verify each change.
Faster fixes, fewer surprises, and a Microsoft 365 environment you can trust Copilot to index.
.avif)
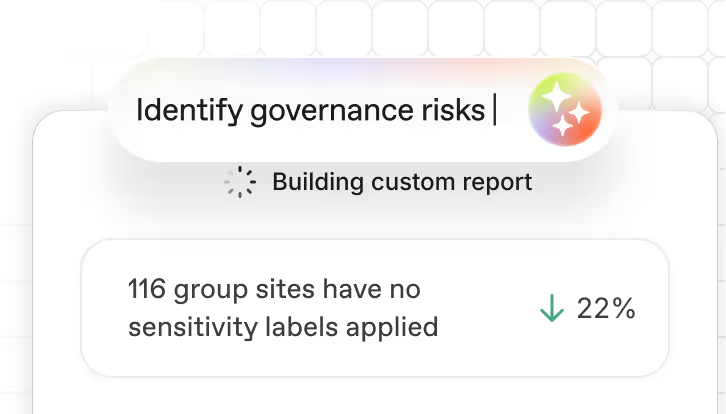
Turn insights into improvements
ShareGate Protect gives you the reports and insights to prove that your tenant is secure enough to ensure your end users can leverage AI without endangering your sensitive data.
- Identify access and sharing patterns that could expose sensitive content to Copilot.
- Focus on the data sources that need attention with smart recommendations.
- Use insights to continuously adjust governance settings as your Copilot adoption grows.
Because when your data’s secure, your organization can innovate with confidence.
.avif)
.avif)
More ways to improve Microsoft 365 governance
Oversharing and access
Oversharing is one of the biggest risks Copilot can amplify. See how Protect helps you spot it early and lock it down fast.
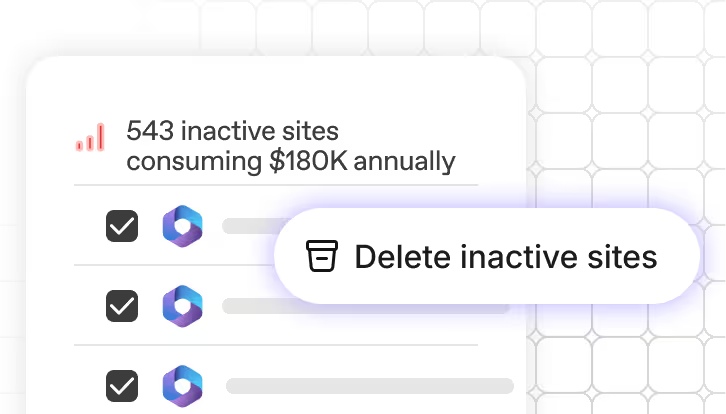
Cost optimization
Find and remove inactive Teams, SharePoint sites, and storage waste before it eats your budget.
Find a partner
Get matched with a certified expert who’ll make your Microsoft 365 journey smoother, faster, and a lot more fun.
Real humans, real fast.
Choosing ShareGate means choosing a highly qualified team of tech support. We’re always there for you.
Microsoft 365 Copilot security FAQs
Microsoft Copilot can access anything your users can: files, chats, emails, teams, SharePoint sites, OneDrive folders, and more. If a user has permission to open it, Copilot can index it and surface it in an AI-generated answer. That’s why oversharing, lingering guest access, and outdated permissions can quickly turn into AI exposure—Copilot doesn’t know what’s sensitive unless your governance does.
ShareGate Protect shows you exactly what Copilot can access across Microsoft 365. It identifies risky sharing, open links, inactive workspaces, and other conditions that could expose sensitive information to Copilot. Then, with in-context remediation, bulk fixes, and smart recommendations, you can lock down risky access fast and keep your environment safe as AI adoption grows.
The biggest Copilot security risks come from existing governance gaps—not Copilot itself. Common issues include:
- Overshared or public links that expose sensitive files
- External guests who still have access they shouldn’t
- Inactive Teams and SharePoint sites with old data Copilot can surface
- Overly broad permissions, like “Everyone” or “All Company”
- Lack of visibility into who can access what
Copilot amplifies whatever access model you already have, which is why proper governance is critical before and during adoption.
You're Copilot-ready when you've cleaned up oversharing and data quality issues. Copilot surfaces anything users already have access to, so if permissions are a mess or content is outdated, that's what Copilot will find.
Run a tenant-wide governance assessment to identify oversharing risks like public groups, "Everyone except external users" access, and sharing links. Also flag inactive sites and outdated content that could make Copilot responses inaccurate or irrelevant. Fix those issues before rolling out Copilot broadly, or it'll surface sensitive information to unintended users and recommend stale content nobody needs.
Yes, but the control point is access permissions, not Copilot settings. Copilot surfaces anything a user already has access to, so use ShareGate Protect to identify and fix oversharing first—find public groups, "Everyone except external users" permissions, and broad sharing links, then remediate them at scale.
Microsoft also provides controls to restrict Copilot reach: restricted SharePoint search, sensitivity labels (including a "no Copilot" label option), and blocking content analysis services. But if users have direct access to files through permissions, those controls won't stop them from opening files manually. They just prevent Copilot from surfacing them in responses.
Yes. Copilot respects Microsoft Purview sensitivity labels when deciding what content to surface. Labels can include a "no Copilot" restriction that specifically prevents Copilot from accessing labeled content, even if users have permissions to the files.
Sensitivity labels are a key Copilot control, but they're managed in Microsoft Purview, not ShareGate Protect. Protect focuses on fixing the oversharing and permissions issues that determine what Copilot can surface, which is the bigger problem for most organizations getting ready for Copilot.