Your Microsoft 365 access control solution
Because not knowing who has access to what isn’t an option anymore.

Trusted by 100,000+ IT pros
Permissions matter on Microsoft 365. Oversharing proves it.
Every file, team, and SharePoint site starts with good intentions. But over time, links stay open, guests keep access, and inactive workspaces linger.
ShareGate Protect helps IT teams uncover risky access, fix it in context, and prove progress with clear, shareable reports.
See the invisible
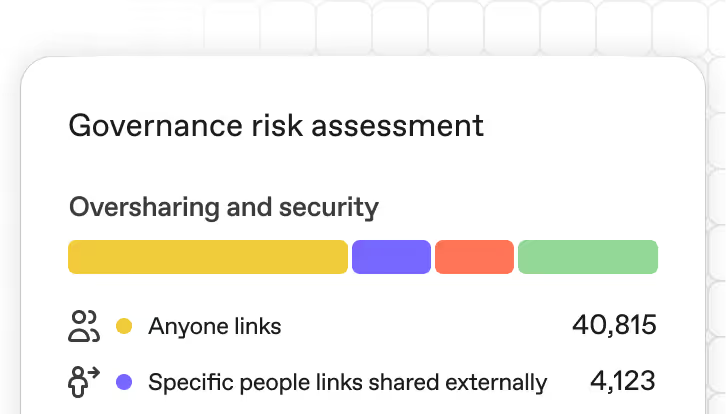
ShareGate Protect—powered by our built-in Governance risk assessment and the classic Permissions matrix report you know and love—cuts through your Microsoft 365 clutter to reveal every place data can leak.
- Find links that never expired.
- Spot teams and sites with outdated permissions.
- Identify guests who no longer need access.
- Detect broad “Everyone” and “All Company” groups that expose too much.
Get one clear view across Teams, SharePoint, OneDrive, and Entra ID. No scripts, no manual exports, no guesswork.
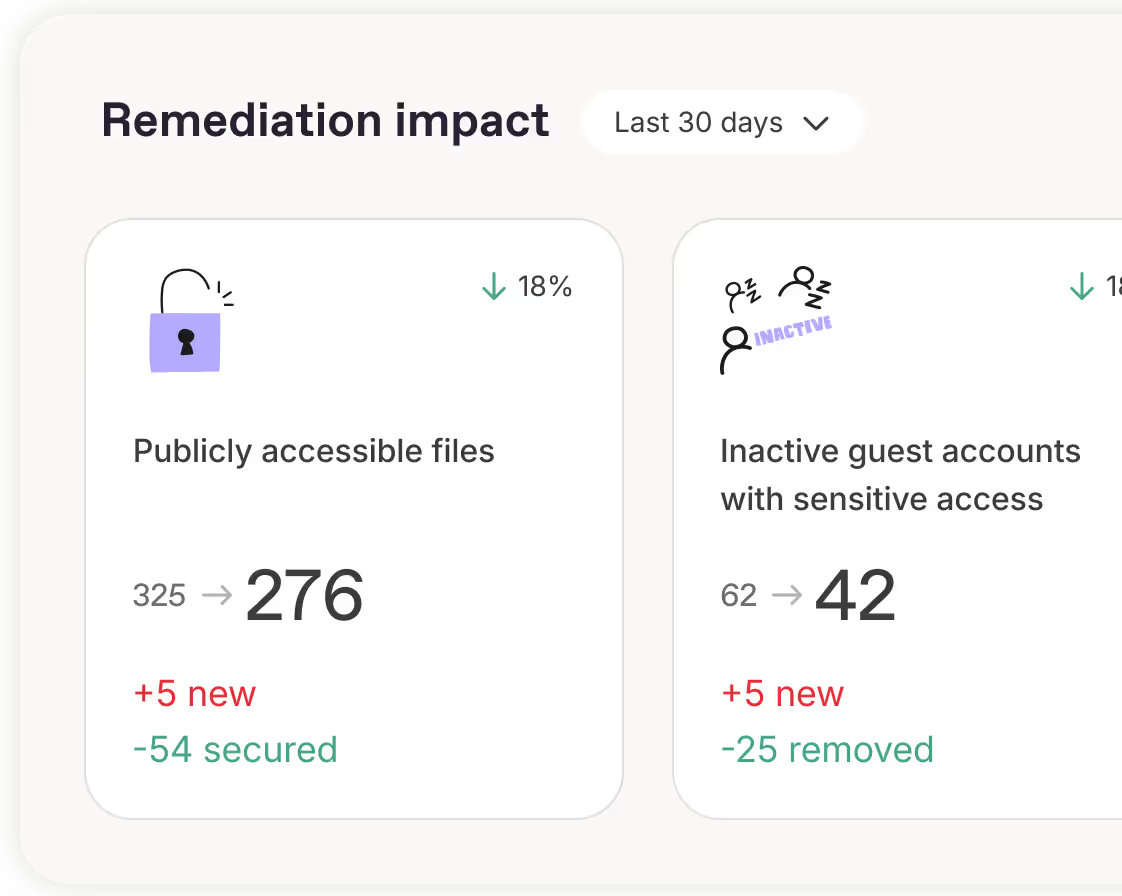
Fix issues fast
ShareGate Protect helps you move from “we found it” to “we fixed it.” With smart recommendations and in-context remediation, you can resolve issues where you find them.
- Prioritize your fixes with smart recommendations.
- Review permissions in context.
- Use bulk actions to clean up faster.
- Remediate safely inside Microsoft 365.
No scripts. No switching tools. No confusion. Just fast, reliable fixes that fit the way you work.
.avif)
Turn insights into improvements
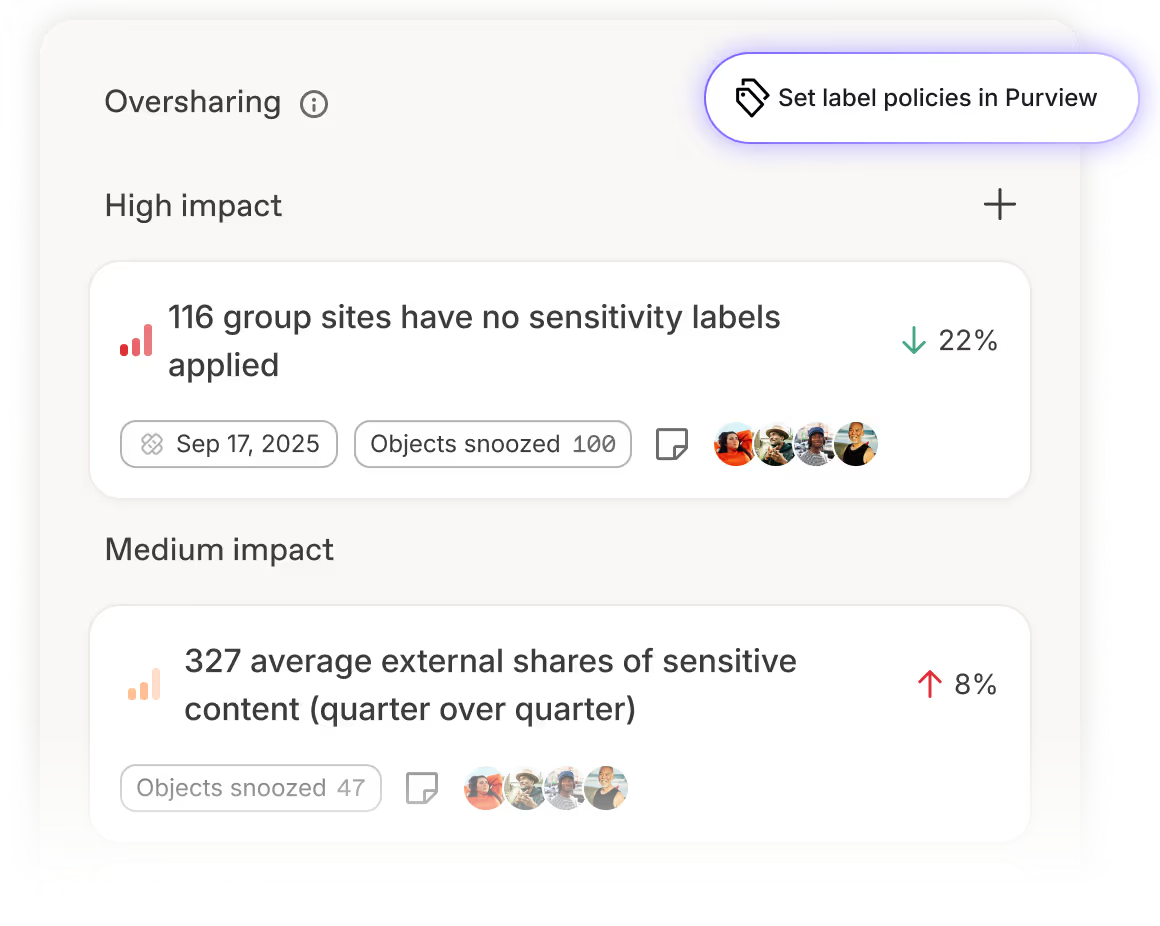
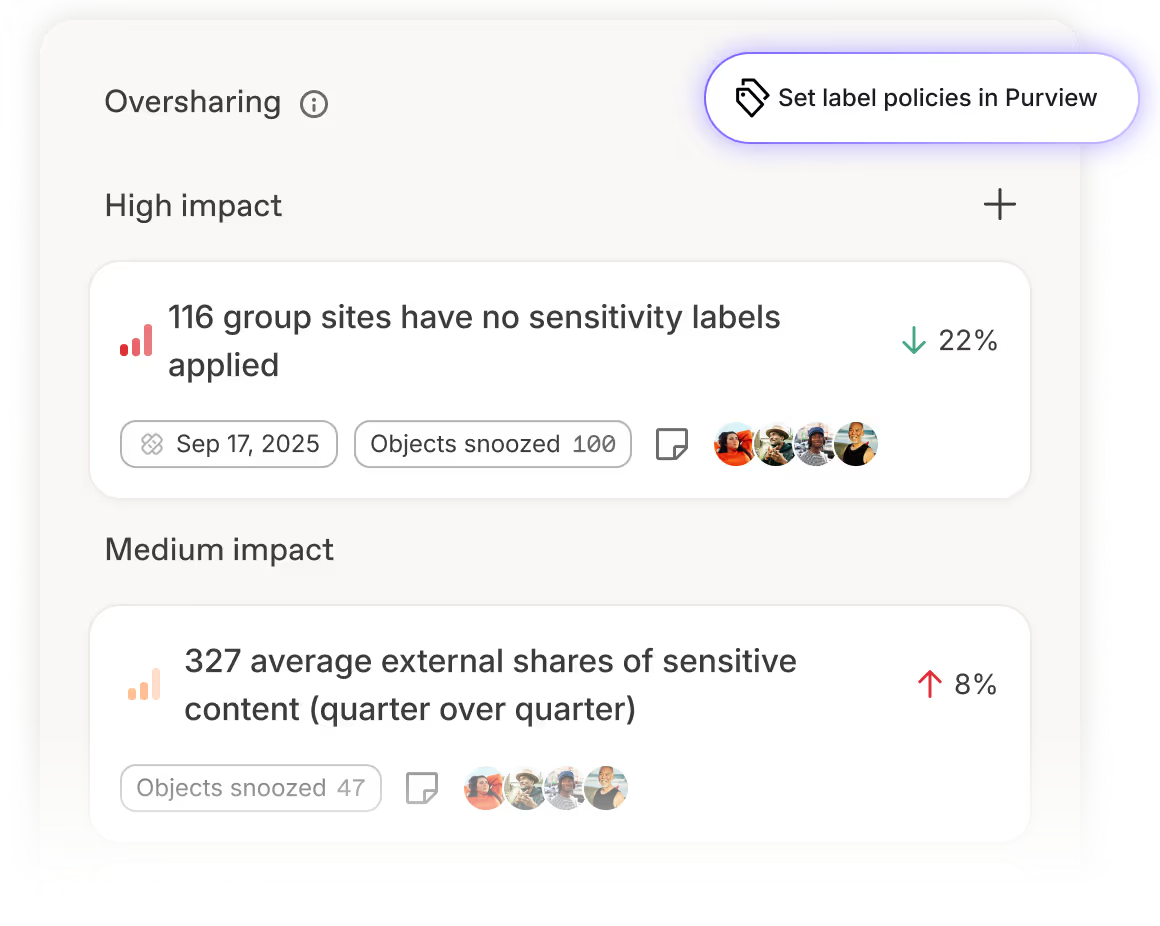
Strengthen permissions and sharing over time. With Governance risk assessments and smart insights you can continuously refine who has access to what.
- See permission trends and recurring oversharing patterns.
- Focus on high-impact areas like guest access and public links with categorized insights.
- Fine-tune sharing and access policies with smart recommendations.
- Track progress as your tenant gets safer and easier to govern.
ShareGate Protect helps you keep Microsoft 365 access right-sized and resilient—so collaboration stays secure, not static.
Take control of Microsoft 365 permissions and external sharing
AI Security
ShareGate Protect helps you keep Copilot from indexing sensitive or overshared data.
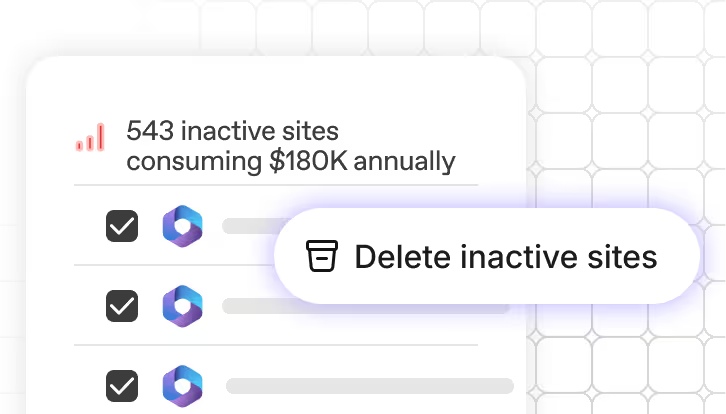
Cost optimization
Find and remove inactive Teams, SharePoint sites, and storage waste before it eats your budget.
Find a partner
Get matched with a certified expert who’ll make your Microsoft 365 journey smoother, faster, and a lot more fun.
Real humans, real fast.
Choosing ShareGate means choosing a highly qualified team of tech support. We’re always there for you.
Microsoft 365 access and sharing FAQs
Oversharing usually happens gradually. As teams grow and projects change, links stay open, guest users keep access, and permissions don’t get reviewed often enough. Broad groups like “Everyone” or “All Company” also make it easy for sensitive files to be shared more widely than intended. Without continuous Microsoft 365 access reviews, these small gaps add up to real data exposure risks.
ShareGate Protect gives you one clear view of who has access to what across Teams, SharePoint, OneDrive, and Entra ID. Its Governance risk assessment highlights oversharing, outdated permissions, and risky guest access. From there, you can use in-context remediation, bulk actions, and smart recommendations to clean things up quickly and keep permissions right-sized over time.
Yes. ShareGate Protect identifies inactive or unnecessary guest accounts across Teams and SharePoint so you can remove or review access with confidence. You’ll see which guests still have permissions, where they have them, and whether those workspaces are still active—making guest access management simple and reliable.
Oversharing is when content is accessible to more people than necessary, usually through broad sharing links (like "Anyone with the link") or overly permissive group memberships. It creates security and compliance risks because sensitive files become accessible to unintended users inside or outside your organization.
ShareGate helps identify oversharing by scanning for sharing links, external users, and permission sprawl across SharePoint, OneDrive, and Teams, so you can clean up access before it becomes a problem.
"Anyone with the link" sharing is the biggest risk. Files become accessible to anyone who gets the URL, including people outside your organization. External user access is another common issue, especially when guest permissions aren't reviewed regularly and old access lingers.
Nested group memberships and orphaned permissions also cause problems. Users inherit access through groups they didn't know they were in, and permissions pile up over time without anyone cleaning them up. The result is sensitive content visible to way more people than it should be.
ShareGate Protect crawls your tenant and flags specific exposure risks: public Microsoft 365 Groups, workspaces where "Everyone except external users" has access (which makes "private" workspaces effectively not private), and risky sharing links like "Anyone with the link" or external sharing.
It shows you who created the links, when they were created, and what permission level they grant. Protect surfaces the risks, then lets you decide what's actually too much access and needs to be cleaned up.
Go to Tenant information, then scroll to Oversharing and security. That's where Protect shows sharing links, broad access like "Everyone except external users," and other oversharing risks across Teams, SharePoint, OneDrive, and Groups.
You can also access the Oversharing section directly and click the tiles to filter into specific lists of workspaces or links.
Yes. Protect gives you tenant-wide visibility and lets you remediate oversharing in bulk—not one site or file at a time. You can delete sharing links at scale, fix risky workspace configurations like "Everyone except external users" backdoors, and correct public workspace settings.
Without a tool like Protect, you're hunting through individual sites and libraries manually with no single view of risks and no way to fix things in bulk.
Protect crawls your tenant every 24 hours and tracks trends over time, so you're not just doing one-off cleanups. Some deeper automation is still being built, but scalable remediation for key oversharing risks is already available.





.avif)