What is access governance in SharePoint?

Table of contents
Want to reduce sprawl in your SharePoint environment? Learn the ins and outs of access governance and keep your unruly data in line.
As an IT admin, you know better than most just how easy it is for data environments to become large, unruly messes when there’s no plan in place. Same goes for SharePoint.
Without some form of access governance planning, or dedicated data governance tools for SharePoint, you can very quickly end up with a disorganized environment with high cloud sprawl and increased security risks.
What is SharePoint access governance?
SharePoint access governance is the act of maintaining an efficient and secure environment where users have the permissions they need to carry out their roles effectively. Correct governance should also prevent ‘privilege creep’ – user permissions extending beyond their daily needs, increasing the risk of security breaches.
But how do you begin to manage such an expansive environment?
How to manage SharePoint access?
There are three key elements to a successful access governance approach. You should carefully consider them when building your SharePoint access governance plan:
- Roles and responsibilities – who can create new sites and who can give permission for others to create them?
- Rules – For example, certain documents can’t be edited without permission from an admin, etc.
- Guidelines – to inform processes, like how long unused files are kept before being deleted.
Manual
These three elements are almost impossible to implement manually. Assigning and tracking responsibilities via the admin center isn’t too difficult, nor is setting up rules and guidelines – it’s only when you get things up and running that they begin to get tricky.
Microsoft Power Automate
SharePoint requires you to access admin centers individually to set library permissions, making manual access governance for numerous SharePoint sites extremely time-consuming. Power users might be able to use Power Automate and Power BI as a workaround, but it won’t give you complete visibility and control of dedicated third-party software.
Discover 6 useful examples to save time on approvals, Planner tasks, and more with Power Automate.
Third-party tools
Third-party platforms like ShareGate have been developed by Microsoft experts and provide you with dedicated data governance tools for SharePoint. These tools allow admins to easily audit SharePoint sites from one central dashboard. Some also feature automated reporting capabilities and permission management shortcuts that reduce the time it takes to carry out access management tasks.
So, once you’ve made your decision on how to manage access, it’s time to put a plan in place.
What is a data governance plan?
A SharePoint data governance plan is the formally laid-out structure of how your SharePoint environment is going to be run. It focuses on daily tasks that keep information accessible to those who need it, yet secure from potential threats.
It can also help with compliance, as your SharePoint sites likely deal with data that is deemed sensitive by regulatory bodies. As the foundation of much of your organization’s Microsoft environment, configuring SharePoint for compliance will give you a good base to build on to maintain your regulatory standards.
Here are some points to consider, based on the three elements of access governance we discussed earlier:
- Roles and responsibilities
- Will you have a data governance working group? (A team in charge of the day-to-day upkeep of the SharePoint environment – usually part of the IT team)
- Which teams and individuals need access to what? (Do certain teams need access to secure documents?)
- Decide which team members can handle permissions (Team leads? IT? A specific team member? C-Suite?)
- Rules
- Set limits on who can view, edit, move, archive, or delete documents
- Limit the size of documents team members can upload without permission
- Decide who can create and access SharePoint sites and pages
- Set external sharing rules for SharePoint sites and files
- Guidelines
- How long should external users have access to SharePoint sites before their access is revoked? Consider setting up an automated renewal/review system
- How often should permissions be reviewed overall? (Monthly is a good place to start)
- Look at the requirements of your organization’s regulatory bodies and ensure that your guidelines take compliance into account
Once you’ve decided on these points, it may help to create a simple table with three columns. One labeled ‘Role’, one labeled ‘Responsibility’, and one labeled ‘Name’. Now fill in the list with the main roles in your access governance plan.
Here's an example:
Once this is done, you can begin to look at a more granular policy regarding SharePoint access management. This might include Sensitivity labels, SharePoint integrations, or retention policies that set compliance-based time limits on your sensitive data – automatically deleting it once it becomes too old.
But perhaps the most important area to focus on after building your plan is your end users. They are the people who work with this data on a daily basis. Giving them a better understanding of how to manage, save, and handle the data they use could be the biggest step you take in your journey to access management excellence.
Streamlining SharePoint access management
Using a third-party SharePoint governance tool is crucial for organizations, particularly for those under strict compliance regulations. Microsoft’s standard monitoring and reporting toolset is slightly too clunky for busy IT admins at medium-sized businesses – and almost unusable for IT departments in large companies with plenty of sites.
ShareGate simplifies the process, bringing all your SharePoint site governance into one admin center.
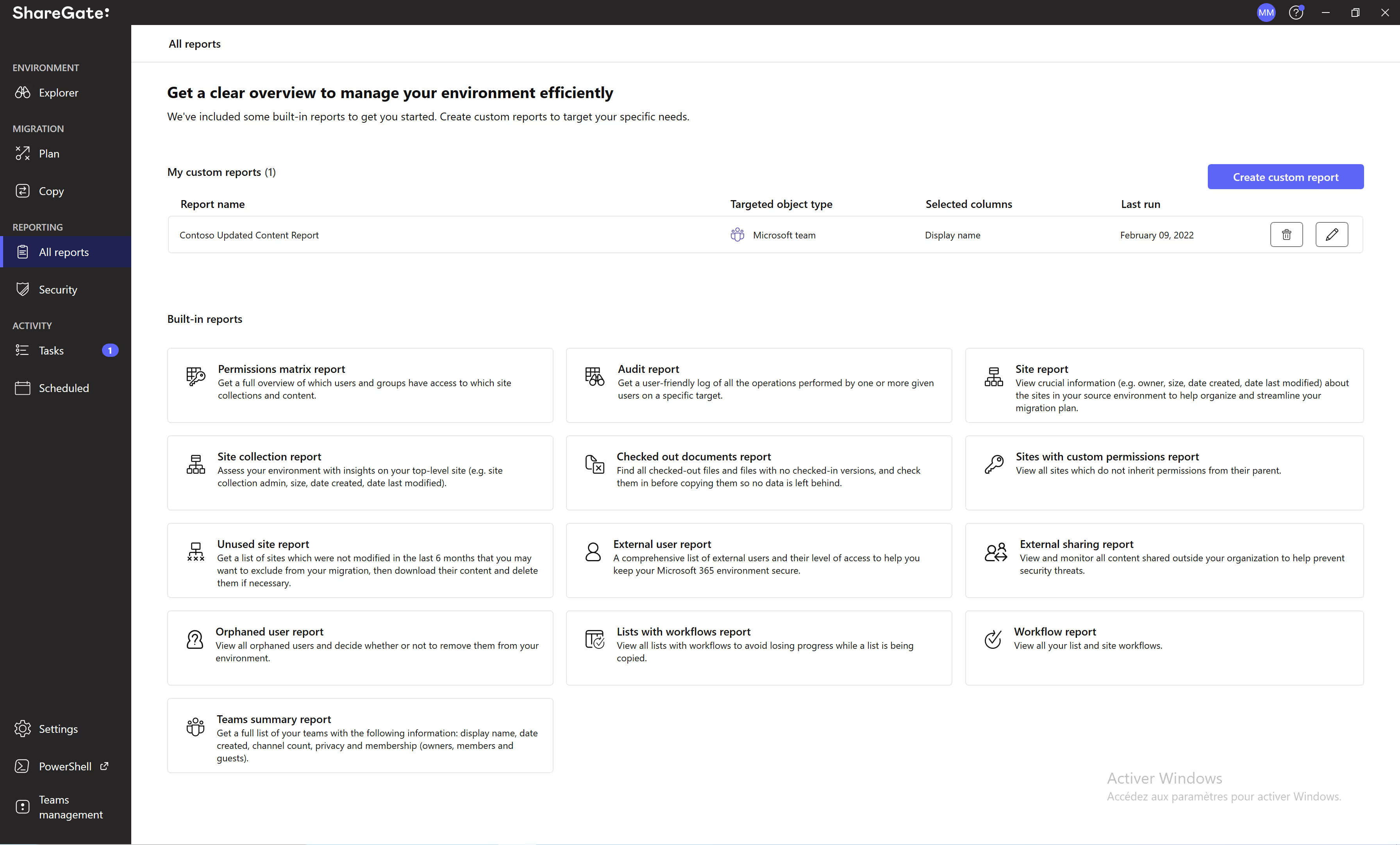
It allows you to monitor permissions across all sites and carry out governance activity straight from the dashboard.
With more reporting options and greater visibility, you can set up a new access governance plan and implement it faster, and more accurately – using data to back up your approach.
ShareGate allows you to scale at speed, without losing track of your data environment, which can cause a security breach or break compliance guidelines.
Find out more about ShareGate’s reporting and permissions management tool or try it for yourself with a 15-day free trial.


.svg)
.avif)
%20(1).avif)